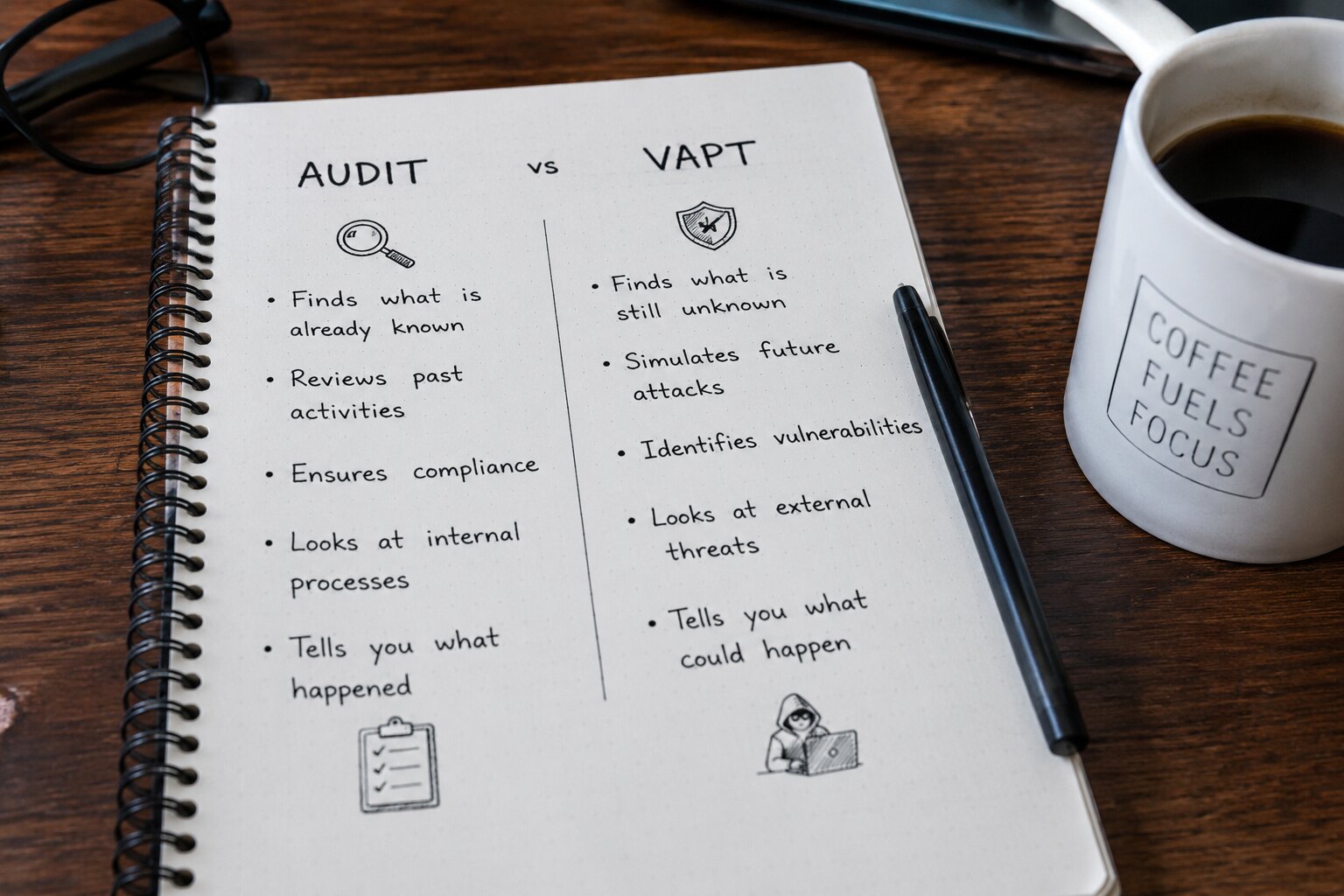
Organisations in Nepal are increasingly hearing about both "security audits" and "VAPT" (Vulnerability Assessment and Penetration Testing), sometimes from regulators, sometimes from auditors, and sometimes from technology vendors. Many people treat these terms interchangeably, but they refer to very different activities with different purposes, methods and outputs.
Understanding the difference helps you make better decisions about your security programme and ensures you are meeting the right requirements.
What Each Actually Means
Security Audit
A security audit is a review and assessment of your security policies, controls, procedures and governance. It checks whether the right security practices are in place and whether they meet defined standards or frameworks, such as ISO 27001, NRB IT guidelines, PCI DSS or your own internal policies.
Audits are primarily documentary and process-based. An auditor reviews your policies, interviews staff, examines configuration documentation, checks access control records and evaluates whether your organisation is managing security appropriately from a governance perspective.
An audit answers: "Do you have the right security controls defined and in place?"
VAPT (Vulnerability Assessment and Penetration Testing)
VAPT is a technical, hands-on testing activity. Instead of reviewing policies and documentation, a penetration tester actively examines your actual systems, applications, networks, servers, APIs, to find technical vulnerabilities and attempts to exploit them to determine real-world impact.
VAPT answers: "Do your security controls actually work? Could an attacker bypass them?"
An audit confirms that your security policy says passwords must be at least 12 characters. VAPT checks whether an attacker could bypass your login system entirely, regardless of password strength.
Side-by-Side Comparison
| Factor | Security Audit | VAPT |
|---|---|---|
| Primary focus | Policies, processes, governance, compliance | Technical vulnerabilities in live systems |
| Method | Document review, interviews, observation | Active technical scanning and exploitation |
| What it checks | Are controls defined and appropriate? | Do controls actually prevent attacks? |
| Output | Compliance report, gap analysis, audit findings | Vulnerability report with exploitation evidence |
| Who conducts it | IT auditors (internal or external) | Certified penetration testers / ethical hackers |
| Regularity | Annual, or as required by frameworks | Annual minimum; more frequent for high-risk systems |
| Technical disruption risk | Very low (review only) | Low if conducted professionally |
| Compliance value | Directly satisfies audit requirements | Satisfies technical testing requirements (NRB, PCI DSS) |
When You Need a Security Audit
A security audit is the right choice when you need to:
- Demonstrate compliance with a regulatory framework (ISO 27001, NRB IT Guidelines, PCI DSS)
- Assess how well your organisation's security governance and policies align with best practice
- Identify gaps in your security programme at a strategic level
- Prepare for certification (e.g., ISO 27001 certification audit)
- Satisfy requirements from clients, investors or board-level governance
- Review third-party vendor security practices before entering a contract
Audits are valuable for establishing a baseline and ensuring your security investment is directed appropriately. They are typically less disruptive than technical testing and can be conducted by your own internal audit team or an external auditor.
When You Need VAPT
VAPT is the right choice when you need to:
- Verify that your web applications, mobile apps or APIs are not exploitable
- Meet NRB requirements for periodic security testing of banking and financial systems
- Satisfy PCI DSS annual penetration testing requirements
- Test a new application or system before launch
- Validate that previous security fixes have been effective
- Understand exactly how an attacker could compromise your systems and what the impact would be
- Reassure customers or clients that you actively test your security
VAPT provides concrete, technical evidence of security, or of weaknesses, that a policy review simply cannot deliver. It is the answer to "we think we're secure, but are we really?"
Why Most Organisations Need Both
A security audit and VAPT are not competing alternatives, they are complementary. An organisation with strong governance but untested systems may have excellent policies that an attacker can bypass entirely. Conversely, an organisation that conducts frequent VAPT but has no governance framework will keep patching individual vulnerabilities without addressing the systemic reasons they exist.
The most effective security programmes use both:
- Audit annually to ensure governance, policies and compliance frameworks are sound
- VAPT at least annually (and after major changes) to verify that controls work technically
- Use audit findings to improve policies; use VAPT findings to fix specific technical vulnerabilities
- Use both together to satisfy regulatory requirements (NRB, PCI DSS, ISO 27001)
Frequently Asked Questions
Most mature organisations benefit from both, used in a complementary way. A security audit reviews your policies, processes and controls to confirm they are in place and appropriate. VAPT then tests whether those controls actually work in practice. Audits without testing leave gaps; testing without governance leaves you patching vulnerabilities indefinitely without addressing root causes.
NRB's Information Technology Guidelines and Cybersecurity Guidelines require both. Banks and financial institutions must have their IT security reviewed through audits aligned to NRB standards, and must also conduct VAPT on their systems at regular intervals. The specific requirements depend on the institution type and risk classification. Consult a cybersecurity professional familiar with NRB guidelines for your specific obligations.
Yes, many cybersecurity firms, including Innomerc Tech, provide both services. However, for formal compliance audits (especially for certification purposes), some frameworks require independence between the auditor and the organisation being audited. For internal security improvement purposes, having a single trusted partner manage both audit and technical testing is efficient and provides consistent, coordinated findings.
This depends heavily on scope. A basic internal security audit can be relatively low cost. ISO 27001 certification audits involve significant effort and investment. Similarly, a focused web application VAPT on a small site costs far less than a comprehensive enterprise VAPT covering networks, multiple applications and cloud infrastructure. Both services are scoped individually, contact Innomerc Tech for an assessment of your specific needs.
Getting Started
If you are unsure which service your organisation needs first, the answer usually depends on your current situation:
- If you have no formal security policies or governance, start with a security audit to understand your baseline and identify the biggest gaps.
- If you have internet-facing systems (websites, applications, APIs) that have not been formally tested, VAPT should be a priority, especially if you handle customer data or financial transactions.
- If you are approaching a compliance deadline (NRB, PCI DSS), speak to a qualified team immediately, both activities may be required within a fixed timeframe.
Innomerc Tech provides both cybersecurity consulting and security auditing alongside VAPT services, and can help you build a security programme that addresses both governance and technical security. Contact us to discuss where to start.